AWS IAM Policy Simulator
Final-year BSc IT student and DevOps Engineer with strong hands-on experience in AWS and cloud-native technologies. I focus on building, deploying, and automating reliable systems using modern DevOps practices.
I have practical experience working with Docker and Kubernetes for containerization and orchestration, Terraform and Ansible for infrastructure automation, and CI/CD pipelines using Jenkins, GitHub Actions, and AWS CodePipeline. I enjoy solving real-world problems related to deployment, scalability, and system reliability.
Test Permissions Without Risking Your AWS Account
When working with AWS IAM, one of the most common questions engineers face is:
“Is this permission enough?”
“Did I accidentally give more access than required?”
Testing IAM permissions directly in a real AWS account can be risky, especially in production environments. Creating users, attaching policies, and performing actions just to verify access can lead to unintended security issues.
This is where AWS IAM Policy Simulator becomes extremely useful.
What Is AWS IAM Policy Simulator?
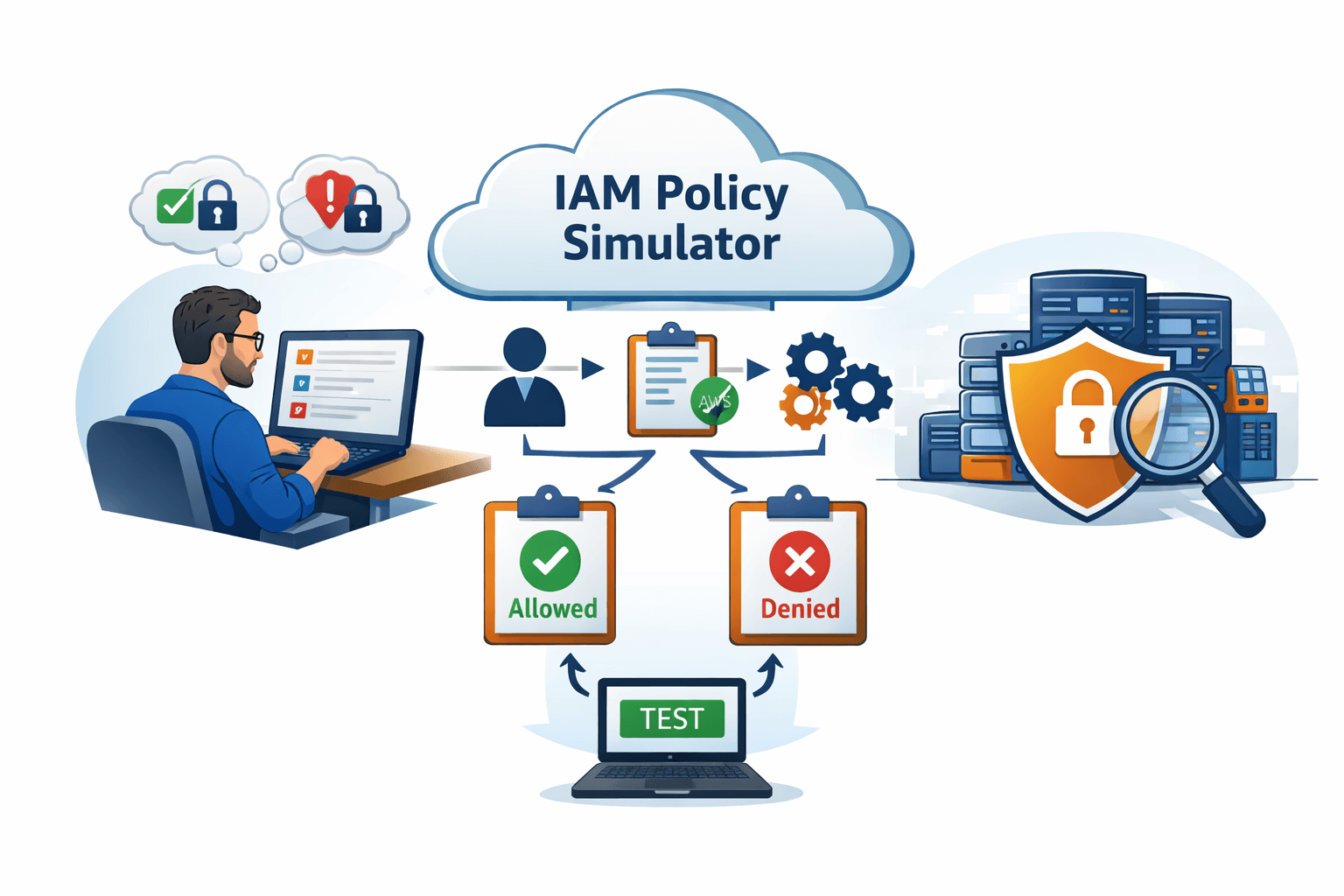
AWS IAM Policy Simulator is a built-in AWS tool that allows you to test and validate IAM permissions without actually creating or modifying resources.
It simulates how AWS evaluates policies and tells you whether a specific action would be allowed or denied for a given IAM user, role, or policy.
In simple terms, it answers:
Can this user perform this action?
Which policy allows or denies it?
All without touching real infrastructure.
Why You Should Use IAM Policy Simulator
1. Avoid Testing in Real AWS Accounts
Testing permissions manually often means:
Creating resources
Triggering API calls
Risking security or unexpected costs
The Policy Simulator removes this risk entirely.
2. Validate Least Privilege Access
IAM best practice recommends granting only the permissions required.
With the simulator, you can:
Check if permissions are insufficient
Detect over-permissioned policies
Fine-tune policies before deployment
3. Debug Permission Issues Faster
Instead of guessing why an action is failing:
Simulate the action
Identify the exact policy causing the denial
Fix the issue quickly
This is especially helpful in complex environments with multiple attached policies.
How IAM Policy Simulator Works
At a high level, the simulator follows these steps:
Select an IAM user, role, or policy
Choose AWS services and actions (for example:
s3:PutObject)Simulate the request
Review the result (Allowed or Denied)
See which policy affected the decision

AWS evaluates permissions exactly as it would during a real API call - just without executing it.
How to Access IAM Policy Simulator
You can access the IAM Policy Simulator using the link below:
https://policysim.aws.amazon.com/home/index.jsp
Steps:
Log in to your AWS account
Open the IAM Policy Simulator
Select a user, role, or group
Choose actions to simulate
Review the results
Real-World Use Cases
Use Case 1: Before Assigning Permissions
Before attaching a policy to a user or role:
Simulate required actions
Confirm permissions are sufficient
Avoid granting unnecessary access
Use Case 2: Troubleshooting Access Denied Errors
When an application fails due to permission issues:
Simulate the failing action
Identify missing permissions
Update policies confidently
Use Case 3: Security Reviews and Audits
During audits:
Validate access paths
Ensure least privilege
Demonstrate compliance without modifying infrastructure
Limitations to Keep in Mind
While powerful, the IAM Policy Simulator:
Does not simulate resource-based policies perfectly in all scenarios
Does not execute real AWS operations
Should be used alongside logging tools like AWS CloudTrail
It is best used as a pre-deployment and debugging tool, not a replacement for monitoring.
Best Practices When Using IAM Policy Simulator
Always simulate permissions before production deployment
Use it to refine least-privilege policies
Combine it with IAM Access Analyzer and CloudTrail
Regularly review policies as services evolve
Conclusion
AWS IAM Policy Simulator is an essential tool for anyone working with AWS security and access management.
It allows you to:
Test permissions safely
Reduce security risks
Debug faster
Follow IAM best practices
If you’re working with IAM and not using the Policy Simulator yet, you’re missing a powerful safety net.
Happy Learning,
Amitabh Soni